This article contains a glossary of backup terms that that are used in relation to backup and restore operations.
What is MD5 hash?
In cryptography, MD5 (Message-Digest algorithm 5) is a widely used cryptographic hash function with a 128-bit hash value.
As an Internet standard (RFC 1321), MD5 has been employed in a wide variety of security applications and is also commonly used to check the integrity of files. However, it has been shown that MD5 is not collision resistant; as such, MD5 is not suitable for applications like SSL certificates or digital signatures that rely on this property. An MD5 hash is typically expressed as a 32-digit hexadecimal number.
What is Public-Key Encryption?
Public-Key Encryption is a scheme using an asymmetric algorithm to create a pair of keys for encryption: a public key encrypts data, and a corresponding private key decrypts it.
In some situations, such as digital signatures, the process is reversed: the sender uses a private key to create a unique number that can be read by anyone who has the corresponding public key. The agreement of the public and private keys verifies that the message is truly from the sender.
What is SHA1 hash?
The SHA hash functions are a set of cryptographic hash functions designed by the National Security Agency (NSA) and published by the NIST as a U.S. Federal Information Processing Standard. SHA stands for Secure Hash Algorithm. The three SHA algorithms are structured differently and are distinguished as SHA-0, SHA-1, and SHA-2. The SHA-2 family uses an identical algorithm with a variable digest size which is distinguished as SHA-224, SHA-256, SHA-384, and SHA-512.
SHA-1 is the best established of the existing SHA hash functions and is employed in several widely used security applications and protocols. In 2005, security flaws were identified in SHA-1, namely that a possible mathematical weakness might exist, indicating that a stronger hash function would be desirable. Although no attacks have yet been reported on the SHA-2 variants, they are algorithmically similar to SHA-1 and so efforts are underway to develop improved alternatives. A new hash standard, SHA-3, is currently under development – the function will be selected via an open competition running between fall 2008 and 2012.
What is a backup software?
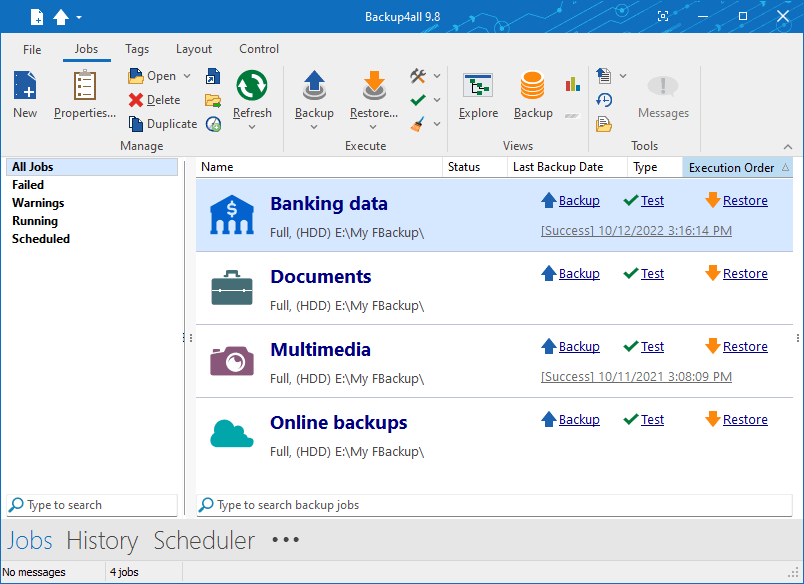
A backup software is a computer software used to perform a complete back up of files, data, database, system or server. The backup software enables you to make an exact duplicate of everything contained in the original source. These applications must also be used to perform a recovery of the data or system in the event of a disaster. Backup4all is such a program, as it allows users to back-up their data with ease.
What is Hyper-V backup?
The Hyper-V role in Windows Server provides software infrastructure and basic management tools that you can use to create and manage a virtualized server computing environment.
When you plan a Hyper-V backup and recovery strategy for a virtualized server environment, there are several factors to consider. You must consider the different types of backups you can make, the state of the virtual machine, and the type of storage being used by the virtual machines.
What is automated backup?
An automated backup is a scheduled backup configured to run daily, weekly or monthly. The backup does not need to be performed manually because the application will start and execute the backup at its scheduled time. A notification email containing the backup log can be sent to an email address. When a problem appears, the administrator will be notified about that by email.
What is a backup procedure?
A backup procedure represents the way you back up your files. Any backup procedure starts with a concept of a data repository. The backup data needs to be stored and organized. Therefore, it's important to establish your backup procedure before choosing the backup solution that is right for you. Different backup procedures have different advantages.
What is online backup storage?
Online backup storage is an offsite server used to store personal data files and folders, or the entire contents of a hard drive which is backed up by multiple computers over the Internet.
What is a backup rotation scheme?
A backup rotation scheme is a method for effectively backing up data where multiple media are used in the backup process. The scheme determines how and when each piece of removable storage is used for a backup job and how long it is retained once it has backup data stored on it.
Different techniques have evolved over time to balance data retention and restoration needs with the cost of extra data storage media. Such a scheme can be quite complicated if it takes incremental backups, multiple retention periods, and off-site storage into consideration. The most widely-known schemes are Grandfather-father-son, Tower of Hanoi, etc.
What is a continuous backup?
Continuous backup, also called Continuous data protection (CDP) or real-time backup, refers to backup of computer data by automatically saving a copy of every change made to that data, essentially capturing every version of the data that the user saves. It allows the user or administrator to restore data to any point in time.
Continuous backup is a service that captures changes to data to a separate storage location. There are multiple methods for capturing the continuous changes involving different technologies that serve different needs. Continuous backup based solutions can provide fine granularities of restorable objects ranging from crash-consistent images to logical objects such as files, mailboxes, messages, and database files and logs.
What is a bare metal backup?
Bare metal backup is a technique in the field of data backup where the backed up data is available in a form which allows one to restore a computer system from "bare metal", i.e. without any requirements as to previously installed software or operating system.
Typically, the backed up data include the necessary operating system, applications, and data components to rebuild or restore the backed up system to an entirely separate piece of hardware.
Bare metal backup differs from local disk image backup where a copy of the disk image, and the backup software, are stored on the computer that is backed up.
Bare metal backup differs from simple data backups where application data, but neither the applications nor the operating system is backed up or restored as a unit.
What is a system backup?
A system backup (or disk image) is a backup of all system files, which allows restoring the operating system to a working state after a crash. Usually, only special programs, targeted on backing up system files, can perform a system backup. Sometimes this term can be interpreted as system registry backup, i.e. backup the system and application settings stored in the registry.
What is tape backup?
Tape backup means to periodically copy the contents of all or a designated amount of data from its usual storage device to a tape cartridge device. In the event of a hard disk crash or hard disk failure, the data won't be lost. A tape backup can be done manually or, with appropriate software, be scheduled to run automatically.
Tape backup systems exist for needs ranging from backing up the hard disk on a personal computer to backing up large amounts of storage for archiving and disaster recovery purposes in a large enterprise as part of a storage area network (SAN), usually combining a hardware and software package.
Tape backup also includes the ability to restore data that has been backed up back to hard disk storage devices when needed.
What is Public Key Authentication?
Public key authentication is the most secure method for SFTP authentication. Public key authentication uses a pair of computer-generated keys – one public and one private. Each key is usually between 1024 and 2048 bits in length and appears like the sample below. Even though you can see it, it is useless if you don't have the corresponding private key.
Example:
<<<
---- BEGIN SSH2 PUBLIC KEY ----
Subject:
Comment: public key
j3KtneI8KnIzFduf08bTD1vauCjhp2RCfjDEkWXINtBsr2qq8J7BYCqoPEmRIUxN
mFD8mSxTWgN3jm6kw5yv5JltzSZIrYAQ9KCWlOU2IW1TlvUGJij4oJJ2JGjig6Qw
3/Koh2CBmVelKz2D+1bibqRN/pq3YtZsMMbO8wJlOp2I0MMRZLgacmyPK8f3Bo/L
nTBXswEvTgsS+O1plW6vCH2gStkG+9iWvlEIeFySijl6rEKjqts0cz5KwDYdPV3i
PsT1xvuvJX7jlLpiDQcna1qQ09jKg6EERi/Eq/loOeE8pmKtx0q6iAH8/10exikQ
K2h0ikjP9hDP//eq8rg49jER1JHrZfQx8NHNQdxsju3j4HfarnlCppbAf8IkclUQ
jnJgVVLfi66EdOkXv+ifJvY3RDzChhF1DG9iMHa1N0+/3B+TUS7/y9cpVlJyNEMI
8jGKLEz3JMypsMTKflJRUf/qt36F06ktwOBlEtGI3pTsR3JPwYp+bUJxPQoJUM3M
CJgyHVFJko86NpneHeqjCwCPaFvFh2YecOE7haXDwWrUQvATdpJBT6U35XiV5jJS
tQCOdhjexlJsxoYlRNM82qHa6oAfGxVyT6sI6XnEfhkf3+d6triEnYQHaxRIRBg4
th5yHi8DGUaKgivqsL167CVEhMFwAQROBs2pKWLeqd2z5xX99ph7SHIBWXP/+Jcf
8L45JEVAFNDzJpl/u0/jC7GcSvjlThMGMe8w0mSPHjtwfkSrIdLXYa9lByZxut1x
yCPbDHQCvn7Bp6AE1gGTlcSlq5T0AjytziJneIwfrMA=
-----END SSH2 PRIVATE KEY-----
<<<
Public-private keys are typically generated using a key generation utility. Both keys in the pair are generated at the same time and, while the two are related, a private key cannot be computed from a corresponding public key. In addition to authentication, keys can also be used to sign data. To access an account on an SFTP server, a copy of the client’s public key must be uploaded to the server. When the client connects to the server, it proves that it has the correct key and access is granted.
The private key never leaves the client machine, and therefore cannot be stolen or guessed like a password can. Usually, the private key has a “passphrase” associated with it, so even if the private key is stolen, the attacker must still guess the passphrase in order to gain access. Public key authentication does not trust any information from a client or allow any access until the client can prove it has the private key.
What is Secure File Transfer Protocol (SFTP)?
The Secure File Transfer Protocol (or SFTP) is a network protocol that provides file access, file transfer, and file management functionality over any reliable data stream.
It was designed by the Internet Engineering Task Force (IETF) as an extension of the Secure Shell protocol (SSH) version 2.0 to provide secure file transfer capability but is also intended to be usable with other protocols as well. The IETF of the Internet-Draft states that even though this protocol is described in the context of the SSH-2 protocol, this protocol is general and independent of the rest of the SSH2 protocol suite. It could be used in a number of different applications, such as secure file transfer over Transport Layer Security (TLS) and transfer of management information in VPN applications.
This protocol assumes that it is run over a secure channel, such as SSH, that the server has already authenticated the client, and that the identity of the client user is available to the protocol.
What is backup disaster recovery?
Backup disaster recovery is the process, policies, and procedures related to preparing for recovery or continuation of technology infrastructure critical to an organization after a natural or human-induced disaster.
Disaster recovery planning is a subset of a larger process known as business continuity planning and should include planning for resumption of applications, data, hardware, communications (such as networking) and other IT infrastructure. A business continuity plan includes planning for non-IT related aspects such as key personnel, facilities, crisis communication and reputation protection, and should refer to the disaster recovery plan (DRP) for IT related infrastructure recovery/continuity.
What is an image backup?
An image backup is a backup of an entire hard drive by means of creating its image and its probable consequential backup. It allows, in case of a disaster, by restoring a disk image to have the exact same system state as on the moment of the initial image backup.
Some backup programs only back up user files, boot information and files locked by the operating system, such as those in use at the time of the backup, may not be saved on some operating systems. A disk image contains all files, faithfully replicating all data.
What are backup types?
The four fundamental backup types are the full backup, differential backup, incremental backup and mirror backup. Full, differential and incremental creates zipped backups while the mirror backup type creates in destination an exact copy of the source files. The backup4all application includes all these four backup types.
What is differential backup?
Differential backup is a backup type that backs-up all changes made since the last full backup.
What is disk cloning?
Disk cloning is the process of copying the contents of a hard disk to another disk or to an image file for later recovery.
What is full backup?
Full backup is a backup of all source files to the destination. It is the starting point of all other backup types.
What is a hot backup?
This is a backup of a database that is still in use (running).
What is incremental backup?
This is a backup type that contains only the files that have changed since the most recent backup (full or incremental).
What is media spanning?
Sometimes, a backup job is larger than a single destination device. In this case, the backed up data must be split into different parts and distributed across multiple media.
What is multiplexing?
Combining multiple backup sources into a single source that can be backed up to a single storage device.
What is multistreaming?
Backing up the same soure to multiple destinations for redundancy purposes.
What is open file backup?
Backing up a file/folder while it is still in use by an application.
What is synthetic backup?
A backup image that is synthesized from a previous full backup and all the incremental backups since then.
What is tape library?
This is a storage system that contains tape drives, slots to hold cartridges, barcode reader to identify cartridges and automated method to move tapes within the system.
What is trusted paper key?
This is a machine-readable print of a cryptographic key.
What is Virtual Tape Library (VTL)?
VTL is a storage device that is recognized just like a tape library to backup software, but actually stores data via other media.


